VicOne/Block Harbor Global VCC recognizes top performers
Recognizes Top Performers Across Four Categories
Press Release, 12 September 2025
What if your car could defend itself before someone else cracks into its systems?
That was the electric tension during the recent Global Vehicle Cybersecurity Competition (VCC), co-hosted by VicOne and Block Harbor. Over 11 days, nearly 500 people from novices to seasoned cybersecurity veterans faced real-world car hacking challenges from firmware hijacks to decoding encrypted vehicle communications. The goal? Train the next generation of defenders for our connected, software-defined vehicles (SDVs).
The Stakes: Why This Competition Matters
- The automotive world is in a tricky spot: legacy vehicles with old vulnerabilities still roam the roads, and SDVs bring modern risks like remote updates, complex networks, and large attack surfaces.
- There’s a major global shortage of automotive cybersecurity talent—experts who can think like attackers and defenders. These competitions are trying to fix that.
- Connected vehicles are everywhere now. From your Over-The-Air (OTA) updates to ECUs (electronic control units) to CAN (Controller Area Network) buses, there are many points of vulnerability. Training under realistic conditions is essential.
What Went Down: Battles, Winners, and Lessons
Realistic, Tough Challenges
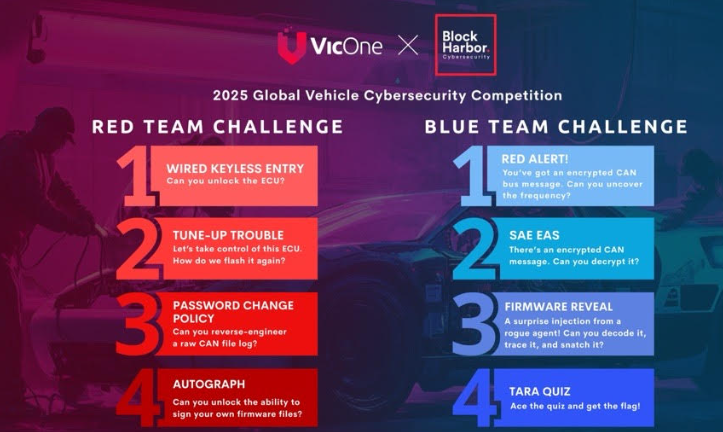
Participants were thrown into “Capture The Flag”-style scenarios built around actual threats. Some of the tasks:
- Cracking open legacy defenses
- Defending against malicious firmware overwrites
- Moving laterally from one ECU to multiple vehicle components
- Protecting cryptographic keys and signatures
- Detecting odd CAN traffic and decrypting communications
- Reverse engineering attacker methods and applying threat modeling (TARA) tools
Who Came Out on Top
Awards were given in four major categories:
| Category | Winner |
|---|---|
| Overall Competition | Willem Melching |
| Blue Team (Defense) | Zsolt Dénes |
| Red Team (Offense) | Chanhyeok Jung |
| Individual Challenges | DK Kong; Kazuki Furukawa; kakur41; Robert Beltri; Song Gyeongsik |
Plus, the overall winner Willem Melching will be flown to Pwn2Own Automotive 2026 in Tokyo—a major stage in the cybersecurity world.
Voices From the Competition
“I’m genuinely surprised by the news, and I’m also really delighted and grateful to have had the opportunity to compete and learn alongside such a large and impressive field of automotive defenders.” Zsolt Dénes, Blue Team winner.
“This was an engaging CTF that brought together reverse engineering, cryptography and exploitation skills. The simulated PowerPC ECU was impressively realistic.” — Willem Melching, Overall winner.
Why the Industry Should Care
Building Real Skills in Real Time
These are more than fun puzzles. They map directly to threats carmakers, suppliers, and even regulators worry about today. Things like firmware integrity, supply-chain security, and anomaly detection in vehicle networks are not future risks—they’re current crises.
Bridging the Talent Gap
With nearly 500 participants, the competition showed there is interest, but more infrastructure is needed training, mentorship, realistic labs. It’s a pipeline approach: catching curious beginners, testing mid-level pros, and pushing elite hackers forward.
Impacts on Vehicle Safety & Consumer Trust
If cars are vulnerable, safety is at risk. If manufacturers can’t prove they take cybersecurity seriously—especially with new rules and public scrutiny—trust erodes. Programs like VCC help set benchmarks, show what good looks like, and force the industry toward higher standards.
What’s Next: From Challenges to Change
- More real-world challenge designs: Expect future contests to simulate even more complex attack surfaces (AI-integrated systems, cloud components, perhaps even edge cases like solar-powered EV vulnerabilities).
- Broader participation: OEMs, insurers, suppliers will want in—both as participants and sponsors/training partners.
- Policy & regulation alignment: Standards bodies will likely watch & learn from what these competitions expose (weaknesses in firmware signing, encrypted communication, etc.).
- Learning doesn’t stop at the contest: Winners and participants will bring knowledge back to their teams, helping improve defenses across the ecosystem.